When voice over internet protocol (VoIP) phone systems were first introduced, security was rarely a concern or even a consideration. Most businesses focused on the benefits, such as low cost, quality, and reliability. Unfortunately, though, VoIP systems are a potential weak spot when it comes to security.
When we think of phone hacks, we generally think of journalists. However, cybercriminals also use phone hacking to access information. They might eavesdrop on calls, access stored private data, or listen to voicemails to get behind-the-scenes industry information. There’s even toll fraud, where hackers use a VoIP system to make expensive calls. Sometimes, the cost of these is in the thousands.
It’s not just about the VoIP system itself. Using exposed entry points in your VoIP setup can give hackers access to your entire business network.
Needless to say, security when using a VoIP phone system is vital. Here are the best ways to stay safe and protect yourself, your team, your customers, and your business.
1. Encryption, encryption, encryption

If there’s one function every digital tool needs to provide, it’s end-to-end encryption. Your VoIP system is no different. If you’re looking at a VoIP product and it doesn’t offer this bare minimum, walk away.
A reliable VoIP setup will provide, as standard, the following encryption support:
- Transport layer security
- Secure real-time transport protocol
However, even some of the biggest names in VoIP only provide these features as an upselling option rather than a base function. If you opt for the cheapest VoIP provider, then you’re going to run serious security risks.
If you want your business calls to remain private, your choice of VoIP system will be critical. End-to-end encryption is not something that’s ‘nice to have’. It’s a core VoIP requirement that will dramatically boost your cybersecurity.
2. Defend your access points
Hackers will always try to find the easiest ways to access business systems. The harder you make it for them, the more likely they’ll head off in search of easier prey. By defending your access points more robustly, you can dramatically cut down your exposure to cybercrime.
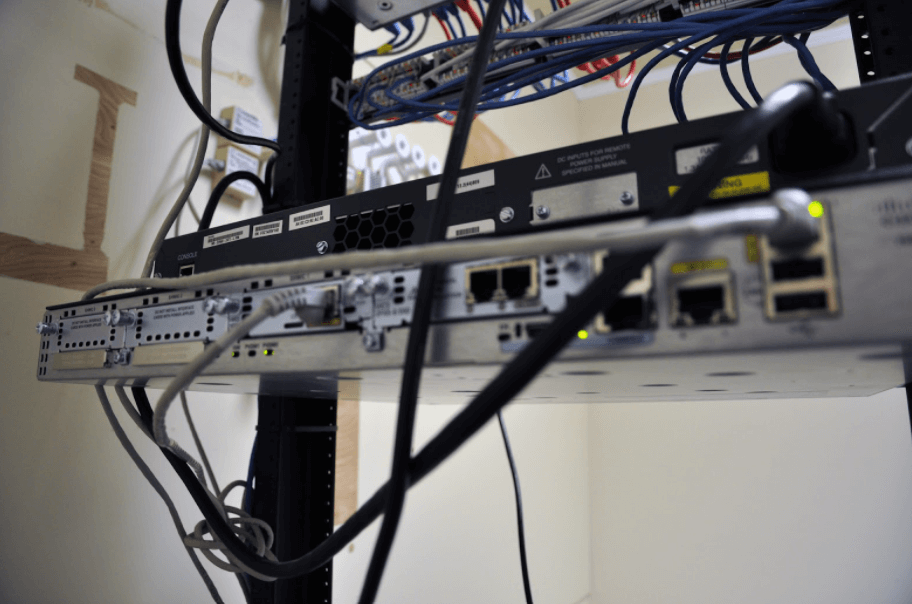
Start by disabling access to your private branch exchange (PBX). A PBX is an essential component for businesses using VoIP who want to have a private telephone network within their business architecture.
There’s also the most basic security protocol that every business needs to have in place: staff training. This is essential if you want your data to be protected when adopting new workplace technologies.
Make sure employees and leaders alike are fully aware of the need for strong passwords that are changed regularly. Simple password management can be the best way to protect your access points.

3. Get physical
A more physical approach to VoIP security is often dismissed. The focus tends to lean so much toward access points that the more secure defensive option can be overlooked. Physical security is your best resource to defend against hackers and criminal opportunists.
Make sure you have the following in place:
- Firewalls. These should be used alongside an IPS to enhance protection for all of your systems, not just your VoIP. A common mistake is to install a firewall but position the VoIP outside of it. If that sounds familiar, an alternative option is to have a dedicated VoIP router with an inbuilt firewall.
- Locked servers. In these days of cloud and hybrid work environments, firewalls and an IPS aren’t always going to be enough. You need to physically lock your servers while centralizing your admin and use domain restrictions. The best way to do this is through two-factor authentication.
- VPN. A virtual private network (VPN) is now a common element in a modern business setting. As workers have become more remote in recent years, they must also use VPNs.
- OS updates. Any updates to your VoIP system will need to be implemented immediately. Often, these updates are a direct response to a new threat. If you don’t update when prompted, you could be leaving your system exposed.
This granular approach to security covers all of the bases and makes it much more challenging for hackers to force their way into your digital setup.
4. Monitor your network
All businesses that use VoIP will – or should – have some form of network monitoring in place. Primarily, this is intended to ensure that call quality is consistent. However, it should also be used to accurately monitor system traffic. With consistent monitoring, any anomalies can be identified quickly.
Criminals often try to access systems at times of the day when they guess there are very few people using the system. Night hacks and weekend attacks are frighteningly common. That’s why network monitoring that uses a combination of real people, a checkable call log, and an automated warning system is valuable.
Consider the alternative. You don’t monitor your network and someone with crime in mind manages to break through your defenses. You don’t know, and it may be a long time before anomalies are spotted. That gives those hackers the time they need to do whatever nefarious activity they like.
5. Response plan and minimization protocol
There are plenty of ways you can fall prey to a cyberattack. If someone is intent on breaking into your system, it can be hard to avoid. Unfortunately, security breaches happen to the best of us.
Knowing that, it’s important to have a response plan in place. Should your system ever become compromised, you’ll have a step-by-step response to the attack. The goal in the event of any breach is to minimize the duration of it and how much damage can be done.
Say you’re on a three way call with suppliers and stakeholders. You spot anomalous activity and implement your action plan. Your system is locked down, and all of the users are purged. While this may affect workplace productivity, it’s also going to reduce the amount of harm a criminal can do.
One of the most common cybercrimes involving VoIPs is called ‘phreaking’. It’s when criminals sneak onto your VoIP system and use it to make calls. To protect against this, you can adopt the following security measures.
- Have call restrictions in place. When you set up your VoIP system, check through the available call destinations. Block those you don’t need.
- Limit your PBX credit. This is one of the smartest ways to reduce the harm done in the case of a security breach. Those hackers might have managed to break through your defenses, but once they hit a spend limit, they can’t do anything else.
Have defenses in place, and you limit the harm threat actors can do. Have a response plan ready for when the worst happens, and you can reduce the impact hackers have.
6. Check your settings
One of the easiest and most basic mistakes when adopting VoIP is to fail to check the settings. The reason this is such a massive security risk is that most VoIPs come with extremely broad security permissions as standard. You need to go through these and turn off any that expose you to risk.
To do this successfully, go through each setting and assess its value. That’s going to require a thorough understanding of when and how you’ll be using your VoIP system. For example, a basic restriction on who can use it seems fairly obvious. However, it’s common to find permission has been granted to all employees, even if they never need to use VoIP.
Simple permission changes, or even just limiting the destinations to which calls can be made through the system, can immediately strengthen security.
7. Using a VLAN
One of the most common kinds of cyberattacks is a distributed denial of service (DDoS). It’s when an army of bots invade the VoIP system and clog it up. By overwhelming your servers, these bots slow your system down considerably, making communication nearly impossible.
A DDoS attack will be visible if you’re using call logs and network monitoring due to unexpected bandwidth spikes, repeated 503 HTTP Error responses, and dramatically slower service. The problem with DDoS attacks is that they’re challenging to block and difficult to get rid of once they strike.
The easiest way to protect against a DDoS attack is to use VLANs (virtual local area networks). Encryption is always going to be your most useful resource to fight against hackers, but integrating VLANs into your security setup means you can spot the opening moment of a bot attack much more quickly.
By having a VLAN in place, you can block unauthorized data flows immediately, ensuring those bots don’t get a foothold in your system.
Protect your VoIP system every day
VoIP systems are extremely advanced communication tools that offer a wealth of benefits for those that use them. Their versatility, flexibility, and reliability are renowned. Combined with their low cost and ease of use, it’s small wonder organizations of all sizes are making use of them.
VoIP systems are designed with security in mind. They’re not flawless, but they do have in-built security measures that already go beyond the needs of many organizations. However, any online technology is vulnerable to criminals.
Take the time to make your VoIP security as robust as possible. The precautions you take today could be what saves you if you attract the attention of those with malice on their minds.
About the Author
 Jenna Bunnell is the Senior Manager for Content Marketing at Dialpad, an AI-incorporated cloud-hosted unified communications system that provides valuable call details for business owners and sales representatives. She is driven and passionate about communicating a brand’s design sensibility and visualizing how content can be presented in creative and comprehensive ways. Here is her LinkedIn.
Jenna Bunnell is the Senior Manager for Content Marketing at Dialpad, an AI-incorporated cloud-hosted unified communications system that provides valuable call details for business owners and sales representatives. She is driven and passionate about communicating a brand’s design sensibility and visualizing how content can be presented in creative and comprehensive ways. Here is her LinkedIn.









