In ancient times having SAP systems exposed to the internet was very rare. Due to technical challenges and different use-cases, the SAP application servers resided in the shielded environment of the hosting center.
Servers providing services to the employees sitting behind their desktop PCs needed to be cooled down by giant air conditioners. A lot has changed since then. The global pandemic has even lifted the need for exposed web-based services provided by the SAP ICM that are available on the go, and from home offices, but can also be consumed via smartphones and tablets. The security aspect for sensitive data residing in the SAP application needs to be rethought because of the paradigm change.
What is the Internet Communication Manager (SAP ICM)?
The SAP Internet Communication Manager ensures communication between the SAP System (NetWeaver Application Server) and the outside world via HTTP, HTTPS, and SMTP protocols work properly. To put it differently, once a transaction SMICM is activated, the SAP NetWeaver Application Server provides a web server serving as the foundation for web-based SAP technologies like Fiori, WebDynpro, or Business Server Pages (BSP).
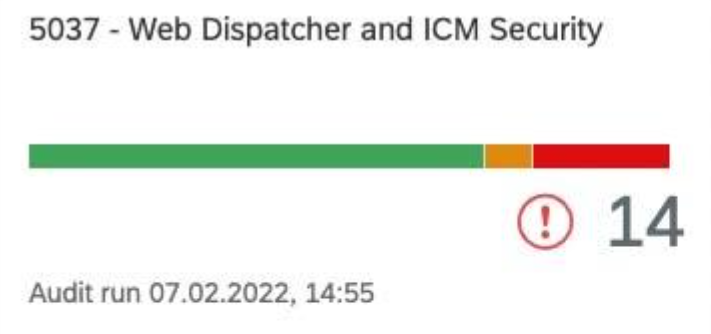
Many security-relevant configurations for SSL encryption, cookie handling and authentication requests (HTTP) come with the ICM. It even provides a dedicated security log. Tools such as SecurityBridge Security & Compliance Management assesse the secure configuration of the ICM in SAP NW and provide guidance for customers to harden the webserver.
Network Segmentation and Service Decoupling
SAP provides various concepts to decouple the business-critical application from the systems providing services to untrusted networks. The SAP Gateway for example may be sitting in the DMZ, which allows exposing various OData services to the outside. The SAP Web Dispatcher provides a solution for web-based access.
The main drive from remote function call towards HTTP is the demand for open infrastructure and accessibility of services. Vital steps to increase security posture are Network segmentation and service decoupling.
Secure the SAP Internet Communication Manager
Having too many services enabled has never been a good practice, but it turns into a security nightmare as soon as connections to untrusted networks exist. In our recent article “Understand and Reduce the Attack Surface” we describe how SAP customers need to gain control and actively manage their security posture with the ultimate goal to reduce anything that is not needed from a business perspective.
Sticking with the Internet Communication Manager (a separate process within SAP NetWeaver Application Servers), it is possible to use system the profile parameters to define whether the ICM is to be started and how it is to be configured. SAP’s Security Baseline template provides additional recommendations to prevent unintended Information Disclosure, e.g. by securing public endpoints not requiring authentication. Depending on the customer-specific scenario,
server port number (profile parameter icm/server_port_<num>) and
HTTP admin port (profile parameter icm/HTTP/admin_<num>) shall be adjusted. Both ports should be protected by SSL over HTTP.
We also confirm the SAP recommendation for the Internet Communication Manager to set an individual error page (see notes 870127 and 1616535 ) that does not disclose relevant information to threat actors.
Enable and configure the ICM Security Log logging
A dedicated ICM Security Log is available for the Internet Communication Manager of SAP NW Application Server and the SAP Web Dispatcher. In newer SAP versions, the log is active by default and can be further tuned by profile parameter “icm/security_log”. The recommended settings according to the security setting of S/4HANA can be found in note 2926224.
Example from SAP Security Baseline Template v2.3:
icm/security_log= LOGFILE=dev_icm_sec_%y_%m,LEVEL=3,MAXFILES=2,MAXSIZEKB=50000,SWITCH TF=month
SecurityBridge customers have a dedicated control for this via the Security & Compliance Management application. For details refer to U5037-0012, “Configuration of ICM Security Log”, which also provides guidance to securely configure your ICM using our best practice settings.
One can neglect concerns about performance, as they are unmeasurable. This log stores security-relevent entries only. The entries are then, for example, of the type “Content filter matched: Permission denied” if a URL filter was applied. Or “NULL bytes in HTTP request”, which is also an indication of HTTPS traffic on the HTTP port. To have the log data available for forensic investigations after an intrusion, it is recommended to store the data log in another system. This is because an attacker may try to cover his tracks by manipulating or deleting the files. Correlation with other log sources is also easier to perform on specialized systems than in the file system or SAP NetWeaver.
Patch SAP ICM Vulnerabilities
While the SAP Web Dispatcher provides dispatching and performance load balancing capabilities, it shares the same code basis with the SAP ICM. Meaning both components may share the same vulnerabilities.
It is not a good practice to rely solely on the security patches, but having no process in place, to ensure timely installation of issued correction e.g. via the SAP Security Patch Day, can lead to security disasters. SAP customers need to sift through their installed base, identifying components needing to be patched. This is particularly important for components like the ICM that expose services to untrusted networks like the internet.
On February 8, 2022, three vulnerabilities, one of them with CVSS 10.0 in SAP Internet Communication Manager (ICM) and SAP Web Dispatcher, were fixed as part of SAP Security Patch Day of February 2022. Consumers affected by a security vulnerability should update SAP security patches as soon as possible. Security Bridge has released SAP Security Patches for June 2022.
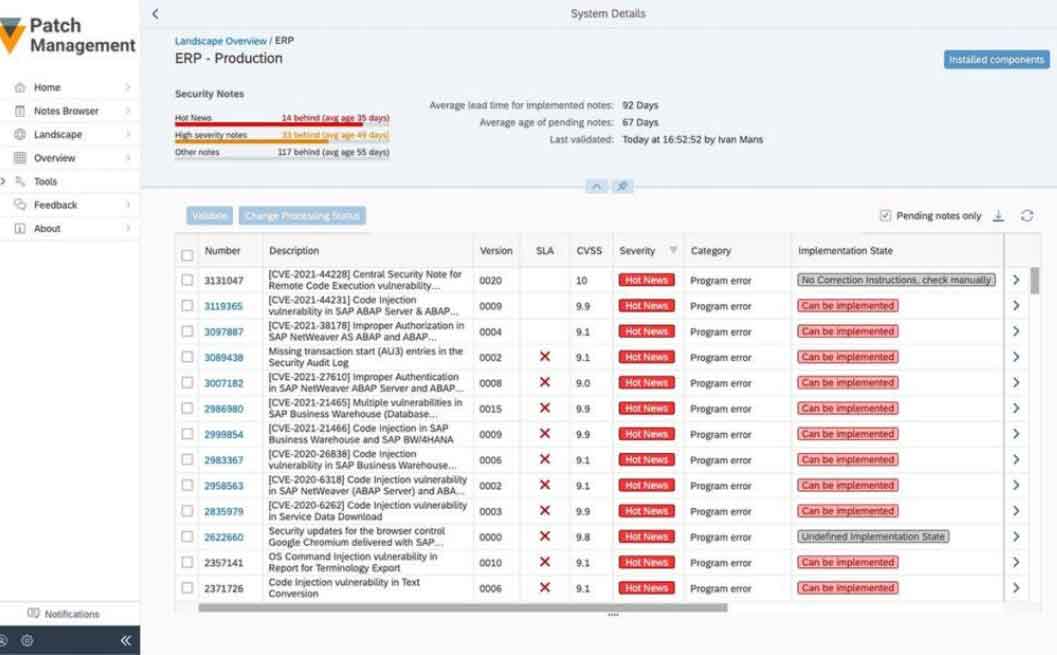
SecurityBridge – Patch Management – System View
Above you can see an example from SecurityBridge Patch Management that provides an overview of missing SAP Security patches.
We recommend that SAP customers – irrespective of the use of an SAP Cybersecurity solution – obtain an overview of missing security updates and install them promptly if possible and in coordination with the necessary departments.
If the installation of a critical fix like “3123396 – [CVE-2022-22536] Request smuggling and request concatenation in SAP NetWeaver, SAP Content Server, and SAP Web Dispatcher” is not possible, please check if a workaround exists to mitigate the risk.