By Bang Ngyuen and David De Cremer
The Internet-of-Things essentially enables mass data collection and analysis, to the benefit not just of businesses, but individuals and society too. However the question is, are businesses behaving ethically when collecting, storing and leveraging this data?
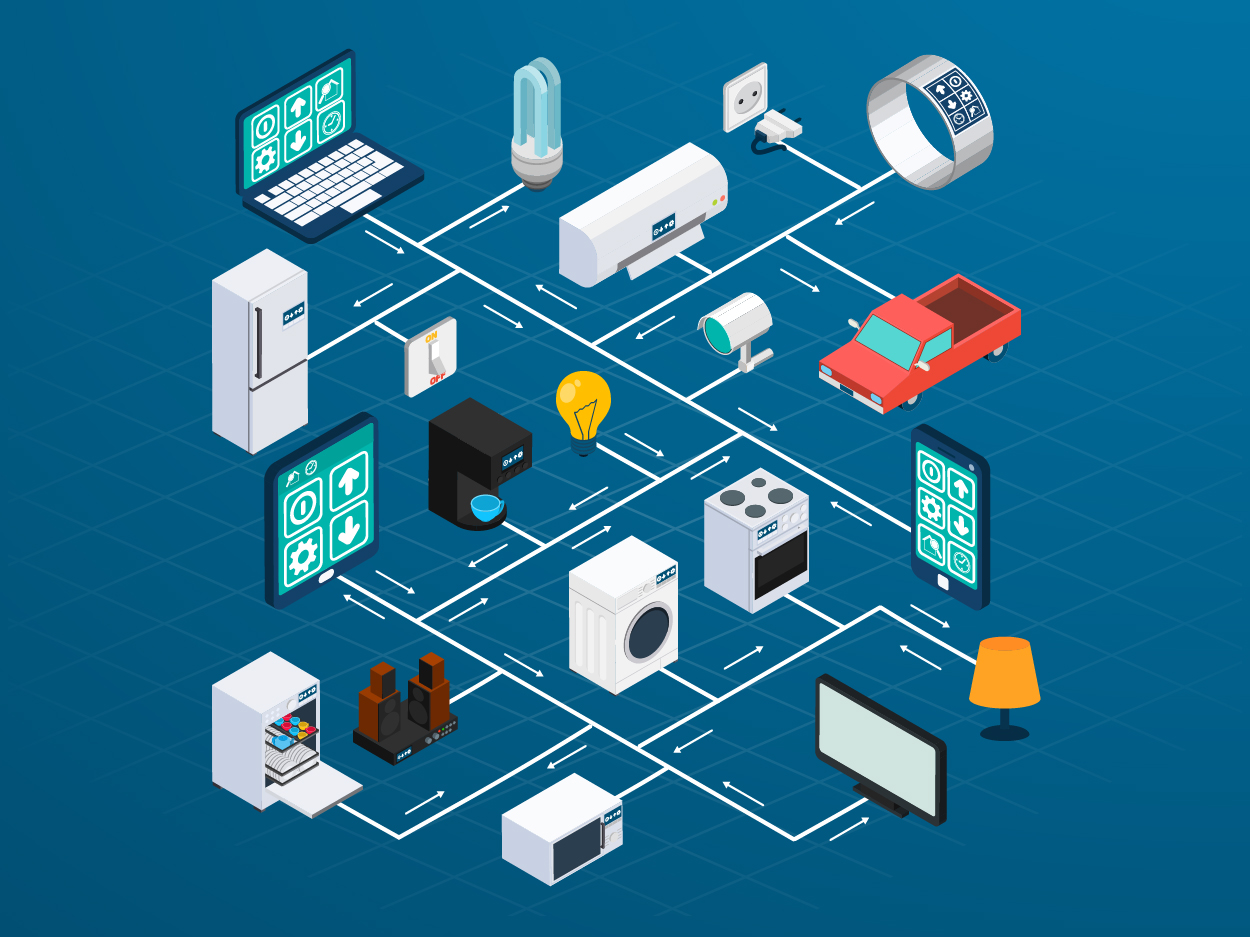
The Internet-of-Things (IoT) revolves around interconnected devices, systems and services within the existing Internet infrastructure. The IoT’s value lies in it being able to capture and analyse the data obtained from the sensors at the endpoints of the connected devices. The ability to put all of this data together means that IoT can bring considerable benefits to individuals, businesses and society. Take a look at the following examples:
• Acts of integrating IoT into the health care system can be the implementation of a chip into individuals, for instance with wearable technology, allowing for hospitals to monitor the vital signs of the patient, which could help indicate whether or not serious assessment is necessary.
• For businesses, the IoT can be useful in many different categories including asset tracking and inventory control, security, individual tracking, shipping and location, and energy conservation.
The crux of the IoT is that it allows for communication between devices, allowing extensive data tracking and measurement that makes it possible to predict and subsequently automate logistical processes. Because IoT relies extensively on delivering information to a business to capitalise on the data supplied, a problem of integrity, however, may be around the corner. As Michael Snyder noted, “The Internet allows us to reach into the outside world from inside our homes, but it also allows the reverse to take place as well.” The IoT industry is slowly starting to recognise that their security track record has been poor. High profile cases such as the US Federal Trade Commission (FTC) settlement with TRENDnet revealing that because of poor security practices their Home CCTV system allowed strangers to see, and sometimes listen into, over 700 home security camera feeds, have contributed to this sense of awareness. As a matter of fact, from cameras to industrial controls to GPS systems, the increased connectivity of devices leads to increased security threats and should thus be managed properly by the IoT industry. But, is it?
[ms-protect-content id=”9932″]We fear it is not. In fact, realising that it is increasingly becoming the norm among knowledge driven companies to collect enormous amounts of data to predict the behaviour of their customers, the risk of integrity breaches is only likely to go up. This unfortunate lack of attention to the integrity aspect of the business is further enhanced by the belief that IoT will enhance the firms’ competitive behavior. This means that companies do not shy away from, for example, monitoring and targeting talented people directly. Also, as the research of Ana Canhoto, a senior lecturer at Oxford Brookes University, shows, although the use of personal data to target talented individuals already holds an integrity problem in itself, most practices are considered perfectly legal. For example:
• LinkedIn is used to spot where professional talent is moving, so if a particular company is hiring people with certain skills, such as programming or editorial skills, it can be anticipated that the firm is planning to advance these aspects.
• Foursquare or other geo-tagged posts (location based posts) can give an idea about whether a specific place is becoming a hotspot, so if key staff are travelling to certain locations this might be a sign of something occurring.
• Online presence of employees and suppliers will contain information about what they might be working on, for example, with clues about their projects, workshops, work patterns etc., so the ability to put those clues together will generate a picture of the strategy of the competitive firm.
• Other market information such as company communication and behavioural marketing data from the competition may also provide information about the direction they are headed. Monitoring blog posts can alert changes in market dynamics and give the firm a head start in their preparation for a counter competitive strategy.
Given the prevalence of these practices, which are considered legal and therefore raise no questions anymore about integrity in the minds of those using this technology, it is not surprising to see that trust in the data collection process is diminishing and malicious intentions and practices are widespread and appear to be growing. For example:
• IoT firms deliberately bind customers with contracts to their unique IoT ecosystem, bleeding them with fees and confounding them with fine print. This is a common practice among insurance providers, health clubs, and banks.
• IoT firms confuse and mislead customers into making poor purchase decisions through the use of complicated and detailed rules and conditions of use/sale. Some of those practices include confusing usage rates, high penalties when customers exceed credit limits, overdrafts and payment deadlines, or fall short of minimum balances in bank accounts.
Overcoming Distrust in the Data Collection Process
Although these practices can be considered borderline exploitation (some are simply poor service practices) they do destroy the trust of the end-users (i.e. customers). We argue that one of the main reasons leading to this violation of trust is that the fairness of both the data collection process and the monitoring technology that is used is poorly managed.
Customers may experience that they are treated differently and even deprived from certain services and benefits. For example, vulnerable groups such as the young, elderly or poor may be taken advantage of by firms with malicious intent, in that they can make the IoT system overly complicated and a pricing system so complex that these groups will find it difficult to make an informed decision. It also happens that customers feel that they do not receive a fair share of the pie in exchange of their personal information. For example, extensive R&D into the IoT to benefit the firms may be considered as a focus on creating more value for the firm itself and leave the customers with the lesser value. Finally, customers may fear that the way companies deal with their personal data will violate fair decision-making procedures. For example, firms collecting and integrating information about their customers are hardly ever checked upon in terms of whether they sell this information to other firms without the customers’ knowledge or permission.
All of this makes clear that the IoT industry has to come up with ways that make customers feel safe and perceive that they themselves and their personal information is dealt with in fair ways.
How Can IoT Managers Establish Fairness with Their Counterparts?
So, what can be done by IoT firms to ensure a fair and hence trustworthy relationship is built with its customers? We advise the following guidelines:
• The IoT firm should monitor all customer and stakeholder touch-points in order to ensure that all relationships are managed to benefit all parties. Mutual and fair value for all needs to be created.
• The IoT firm must have clear guidelines against privacy invasion and information misuse, for instance, with permission from the customers to guide how value can be generated from the data. Moderation and fairness is key.
• Consumers need to feel that they are respected and the seller must value their relationship. Such relationships built towards long-term value is mutually rewarding and progressive.
• Customers must receive a consistent message from the firm in an integrated multichannel customer experience. In this case, the customer must be reminded of the co-creation of value that the firm brings.
• IoT firms must be constantly available to the customers with a sufficient and transparent communication system and procedures. Interaction is key and important in maintaining fairness.
In addition, providing a certain degree of control to customers helps to reduce perceptions of unfairness. The IoT is about long-term relationships and the challenge lies in building relationships within the IoT network where all parties feel fairly treated. Carefully building and managing customer expectations not only help to design experiences that are less likely to be perceived as unfair, but also minimise the negative impact when illegitimate situations occur. So, even when security breaches are present, customers are able to understand the situation because the firm has a transparent communication process to keep them informed.
It is important to note that fairness must be a commitment at the strategic level, from the senior management’s influence in the firm’s philosophy and values statement to the front office of customer services. Implementing training sessions to promote the fairness of IoT practices is a must. Finally, although building fairness is a highly participative and time-consuming activity, the level of fairness that can enhance the overall trust in the IoT is forever. With fairness in place, new advancements in the IoT will not be seen as a threat, but rather as an opportunity to reveal more efficiency within the IoT relationship.
About the Authors
 Bang Nguyen is Associate Professor of Marketing at the East China University of Science and Technology, Shanghai, China, and Futurist at Nucleon AI Industries. He is the guest editor of Journal of Marketing Management on the Internet of Things. Previously, he was a marketing educator at Oxford Brookes University, Oxford, UK. He is the author of the book The Dark Side of CRM.
Bang Nguyen is Associate Professor of Marketing at the East China University of Science and Technology, Shanghai, China, and Futurist at Nucleon AI Industries. He is the guest editor of Journal of Marketing Management on the Internet of Things. Previously, he was a marketing educator at Oxford Brookes University, Oxford, UK. He is the author of the book The Dark Side of CRM.
 David De Cremer is the KPMG Professor of Management Studies at the Judge Business School, University of Cambridge, UK. Previously, he was a Professor of Management at China Europe International Business School in Shanghai. He is the author of the book Pro-active Leadership: How to Overcome Procrastination and be a Bold Decision-Maker.
David De Cremer is the KPMG Professor of Management Studies at the Judge Business School, University of Cambridge, UK. Previously, he was a Professor of Management at China Europe International Business School in Shanghai. He is the author of the book Pro-active Leadership: How to Overcome Procrastination and be a Bold Decision-Maker.
[/ms-protect-content]